With the growth of automation and robotization in many industries, from agriculture and delivery drones to self-driving cars, the demand for accurate and affordable navigation is on the rise. When selecting a GPS/GNSS* positioning receiver it is crucial to understand vulnerabilities of these sensors and the effect they could have on the navigation system. For robots and autonomous devices availability is key to ensuring continuous and reliable service. Safety also needs to be considered for robots and drones operating close to people. GNSS jamming or spoofing needs to be detected and flagged immediately so that other sensors can take over.
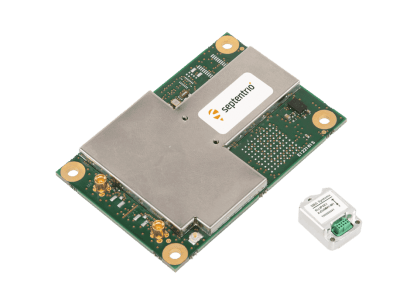
Most autonomous navigation technologies include an Inertial Navigation System (INS), which consists of a GNSS receiver and an IMU sensor. While the GNSS receiver provides absolute positioning in terms of geographic global coordinates, the IMU (Inertial Measurement Unit) measures heading, pitch and roll angles which give orientation information of a moving system.
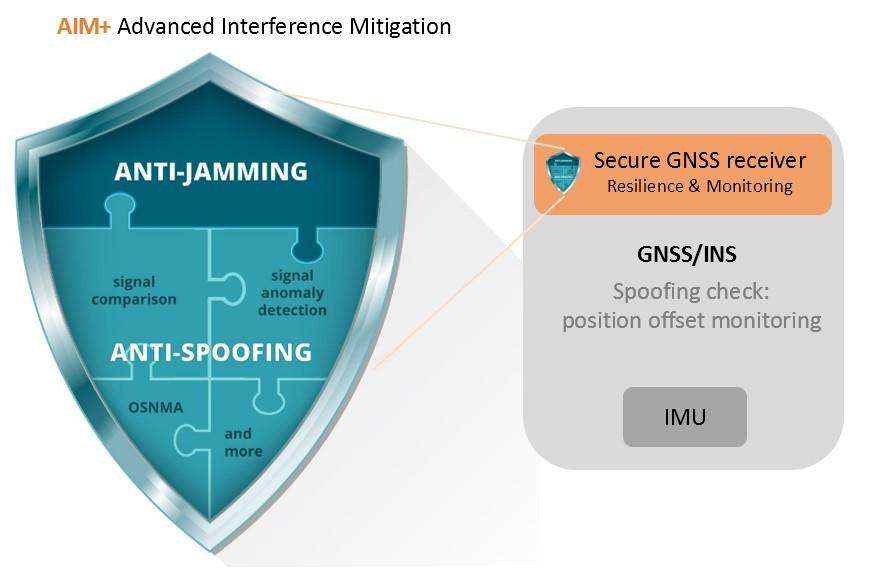
Spoofing is a real threat to GNSS-based INS systems, which is mitigated most effectively by incorporating security mechanisms into all system sub-components. However, since spoofing takes place on the level of the GNSS signal, a number of sophisticated methods can be employed within the receiver to detect and mitigate spoofing. Receivers which are designed with security and robustness in mind, are resilient to GNSS vulnerabilities such as jamming and spoofing. Taking advantage of such robust GNSS technology is also cost effective, allowing companies to focus their development on sensor fusion and navigation.
Jamming and spoofing are real
Jamming is a kind of radio interference, which overpowers weak GNSS signals, causing accuracy degradation and possibly even loss of positioning. Unintentional jamming sources include radio amateurs, maritime and aeronautical radiolocation systems as well as electronic devices located close to the GNSS receiver. There are also intentional jamming devices called “jammers”, which are sometimes found on board of vehicles trying to avoid road tolling.
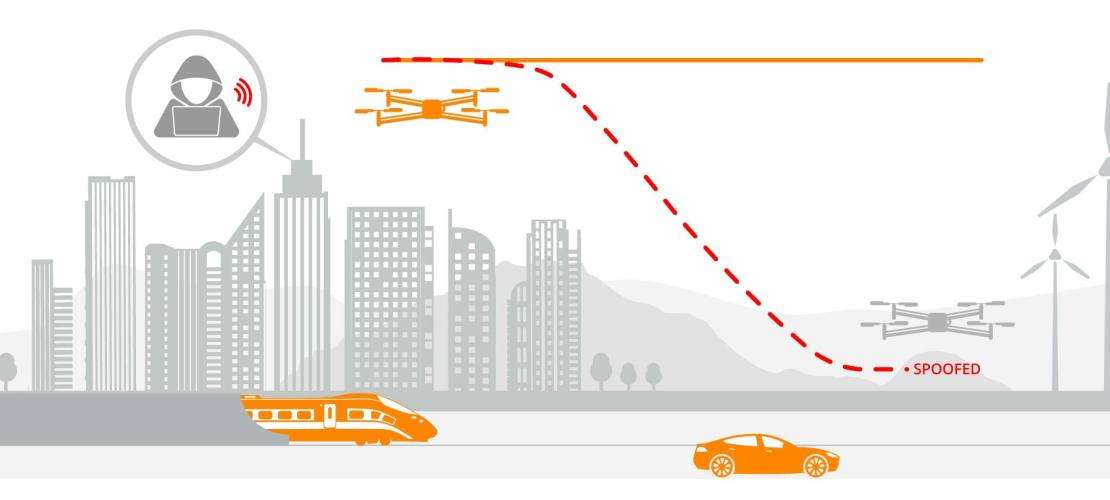
Spoofing is an intelligent form of interference which makes the receiver believe it is at a false location. Spoofing has appeared in the news in a spectacular experiment where a Tesla car was “misled” to take an exit from a highway rather than following the highway as it was supposed to [1]. Consequently, both jamming and spoofing can have an adverse effect on INS systems, which make use of GNSS positioning. For more information on spoofing see OSNMA: the latest in GNSS anti-spoofing security.
How can INS get jammed and spoofed?
While GNSS provides absolute positioning, the IMU measures relative movement, which is subject to cumulative error called drift and needs regular “recalibration”. In a GNSS/INS system both sensors are fused in such a way that the GNSS provides regular IMU “calibration” and the IMU provides angles and extrapolation or “smoothing” of GNSS.
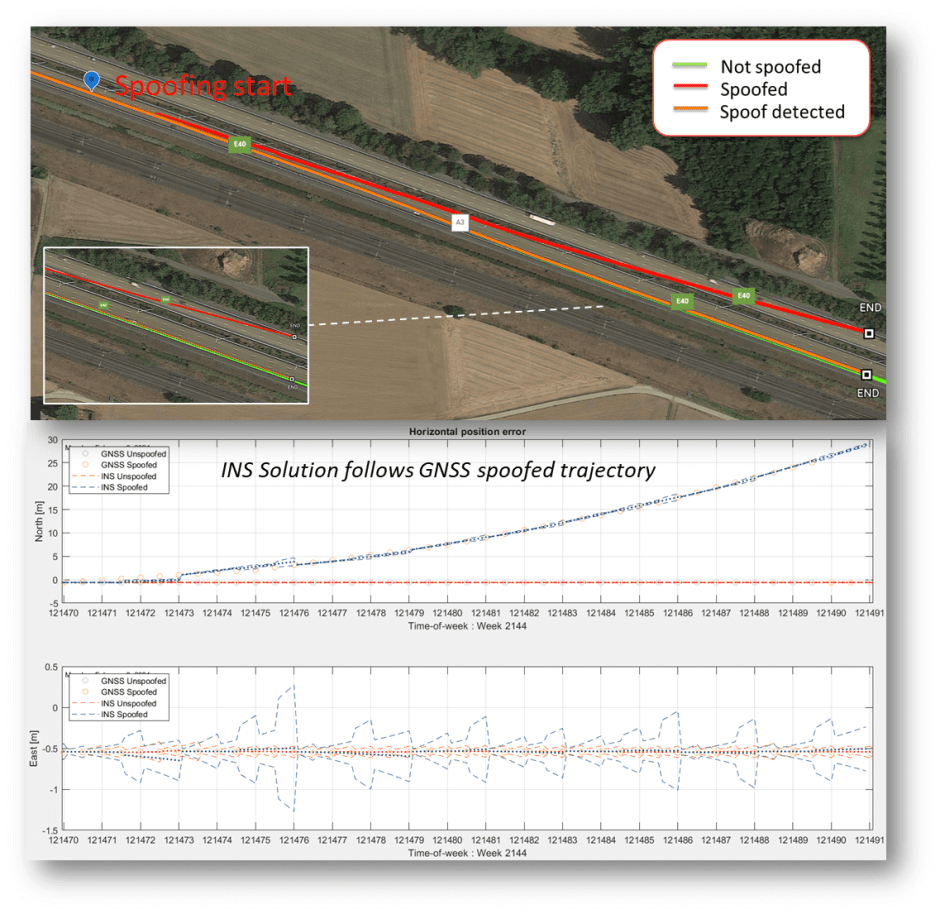
Jamming, which results in loss of positioning, means that the GNSS receiver can no longer be used as part of the INS solution. This can lead to longer INS initialization times or a switch to dead-reckoning mode (IMU solution only), where the position would start to drift. Jamming can also result in measurement outliers, which impact GNSS/INS algorithms (ie. deep or tight coupling). However, it is spoofing which poses the highest security risk for GNSS/INS systems. During a spoofing attack an INS solution could be “hijacked” if the spoofer uses small increments in positioning, which can go undetected by common anti-spoofing methods.
Vulnerability of the common INS anti-spoofing method
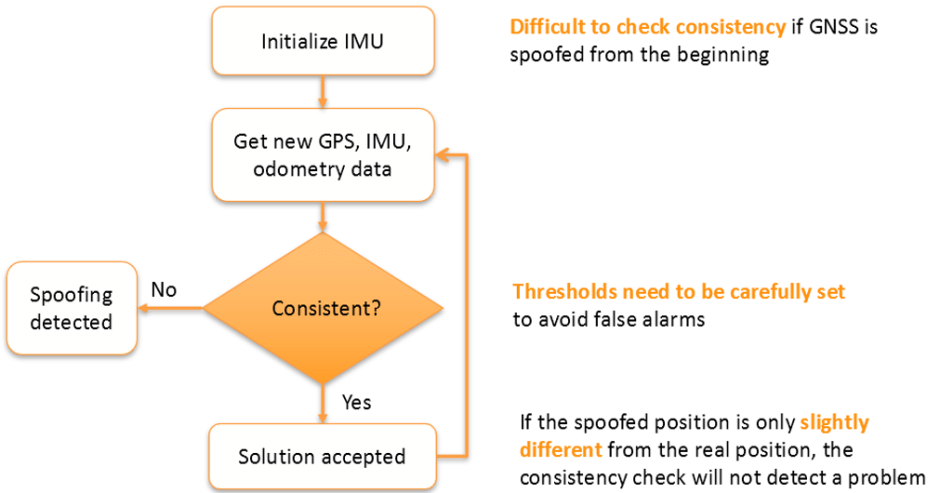
Using sensors other than GNSS such as an IMU or odometry can help flag spoofing by detecting inconsistencies between GNSS and the other sensors. While such sensors help reduce spoofing risks, they are not sufficient to provide full protection because they only output relative positioning which is subject to drift. For example, the GNSS/INS systems can have a drift of a meter or more when visibility of GNSS satellites is lost for longer periods. Spoofers can exploit this drift phenomenon to hijack positioning gradually, in increments comparable to the expected drift.
The diagram below demonstrates a common mechanism used by GNSS/INS systems to detect spoofing. The system is initialized and starts receiving new GNSS, IMU and/or odometry data, which is continuously checked for consistency.